Cyber Security PowerPoint Template
The Cyber Security PowerPoint Template is a professional presentation featuring the Cyber Crime Theme.
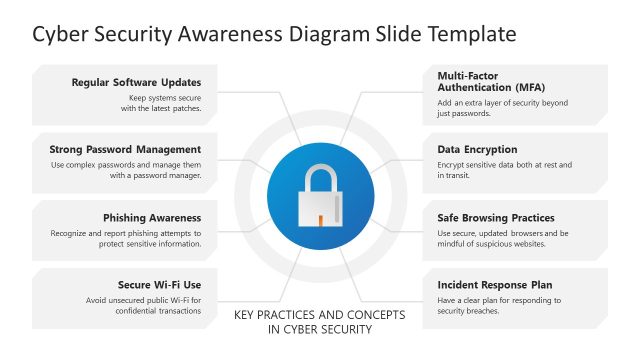
Computers Security, also known as Cyber Security, is the security practices applied to the information systems and infrastructure, networks and data stored or transmitted over them. Modern society reliance and dependence on computer systems has promoted the growth of this field. Computer systems include a wide range of devices and their connecting networks. Some examples include data centers, servers, personal computers, smart devices, smartphones, Internet of Things, Internet, private networks, Wi-Fi networks, Bluetooth, etc.
Computer security involves the set of processes applied to digital equipment, information and services to protect them from unintended or unauthorized access or destruction.
In the modern society new actors appeared, called cyber criminals, which developed illegal practices that exploit systems vulnerabilities for identity theft or other digital criminal activities. In order to secure computer systems, it is necessary to understand the various types of possible “attacks” that can be made against it. The digital attacks are also known as hacks.
The most common hacks known are:
- Backdoors: Secret methods of bypassing authentication or controls.
- Denial-of-Service (DoS): Denial of service attacks make a physical resources or network unavailable to its intended use. Several categories of DoS are designed for different purposes. DoS can be personal or network wide. A common example consists of sending trash request to network ports until the physical machine collapse all its processing power just replying to trash messages.
- Direct Access Hacks: Accessing directly to someone’s (person or organization) digital system and compromising information.
- Eavesdropping (Man in the Middle): This attack consists of listening to private conversations between hosts in a network and compromising sensitive information.
- Spoofing: This technique consist of masquerading as another person (or program) and falsify data.
- Tampering: Malicious modifications to software that generates malfunctions or other vulnerabilities that can be breached with other methods.
- Repudiation: Challenging digital signatures.
- Information Disclosure: Release of sensitive information in an untrusted environment.
The Cyber Security PowerPoint Template will provide the user with professional clipart and backgrounds to create amazing cyber presentations. Ideal for Security and IT Managers, the template is 100% editable.